Have you ever had a bug? It can be frustrating to spend hours fixing something only for it to happen again. In the world of software, bugs are a major issue. Fixing them is costly and time-consuming, but worse yet, if they go undetected, it could result in a data breach or other major security incident.
Even though there’s a lot of work that goes into finding bugs before they happen, it’s worth it to do so. Here are some ways that having a good bug detection process will help your company stay secure and safe from external threats.
The importance of bug detection
Bug detection is very important for any software engineer, but it’s especially crucial when we talk about software that powers critical systems or systems that are potentially connected to critical systems. For example, if you work at a company with mission-critical software, it’s worth it to invest a little more time and money into finding and fixing bugs.
If you’re a web developer, there are bug-hunting tools available that will give you a sense of when you should spend your time and efforts on bugs. Spending some time on eliminating bugs early on will also help your team to avoid technical debt down the road.
Why is bug testing software important?
To make software, especially network-connected software, a high-performing system, it has to be tested to ensure that it’s working as intended. We can, for example, test a device’s Bluetooth functionality to ensure that it works with any other device. Similarly, bug-testing software can be used to do the same thing for software and network functionality.
And while most bug-hunting tools are open source, the results of this testing can be really helpful when it comes to identifying security vulnerabilities. Some bug-hunting tools have the ability to report security vulnerabilities and report that you find something problematic in the software. If it turns out to be a security issue, that security vulnerability can then be closed. You can read more about automated bug testing in this guide to automation testing.
For example, there are a lot of companies that deal with enterprise software. If you have access to these enterprise security tools, you can test software to ensure that it’s secure before it’s rolled out to a business.
What Sort of Bugs Should You Pay Attention To?
Memory leaks
One type of software that we’ll often see exploited in penetration testing is memory leaks. Memory leaks can be difficult to detect and usually the simplest way to identify them is with a source-code search.
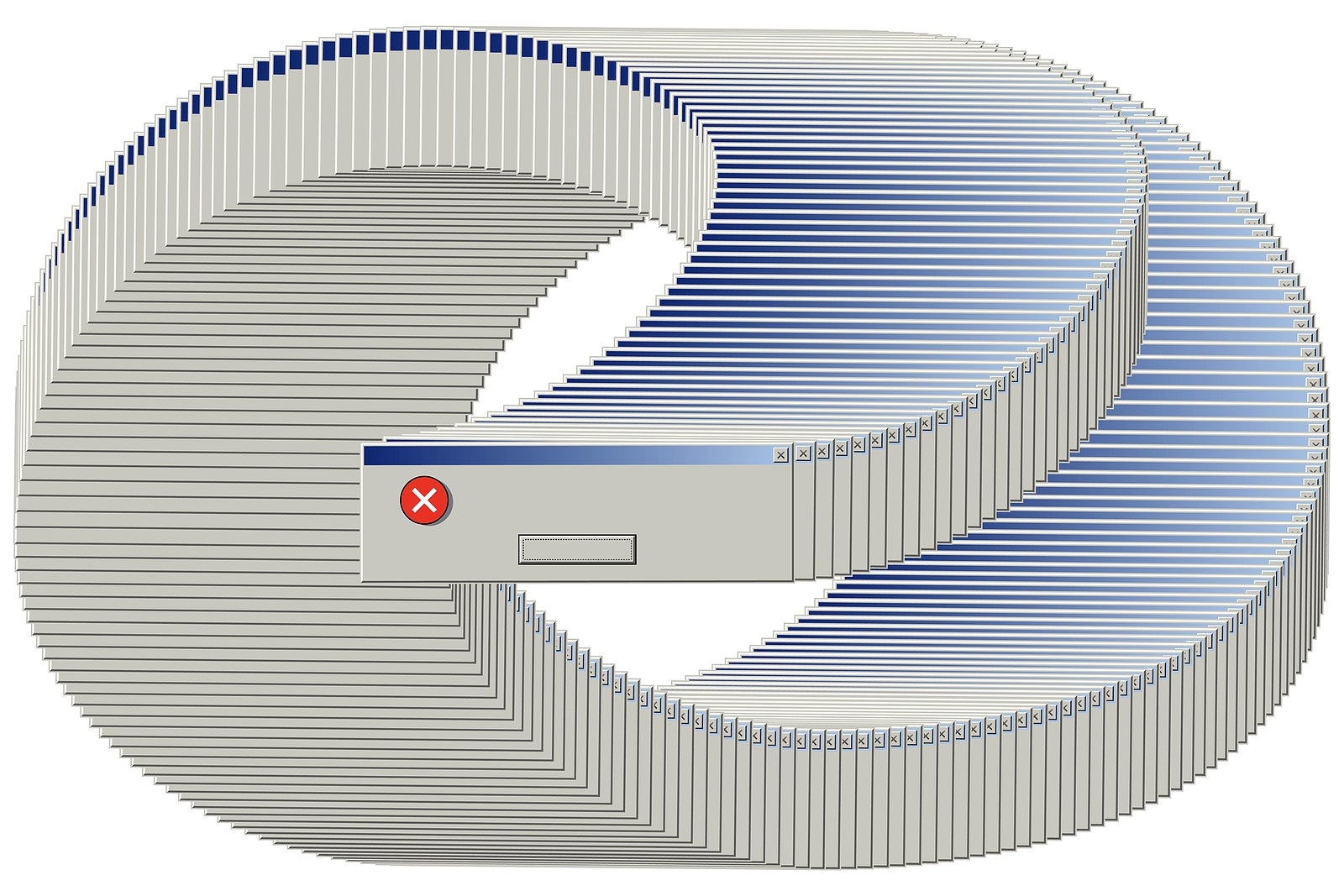
There are many different kinds of memory leaks, but they all have something in common: they’re usually related to IO operations. Examples include improper sharing of data between IO and stack (as seen in the figure below). They can also result from misbehavior on the system, but, in general, memory leaks can happen if a lot of data is used by the application and not used by any other IO operation.
Memory leaks are the kind of bug that can be fairly easy to fix once you discover it. A common solution to the problem of memory leaks is to set up exception handlers that can be triggered by software that is closing files and services in the same manner.
Race conditions
One kind of exploit we’ll see exploited in penetration testing is a race condition. While it’s a common type of exploit, it’s also one of the trickiest bugs to fix because the attacker must have a reasonable expectation that there are no other people on the same network, in the same locations as the victim.
Race conditions are especially hard to spot because they may seem innocuous.
Conclusion
Learning about the kinds of bugs that are commonly found in software is one of the best ways to help you discover and fix security vulnerabilities. It’s also a good idea to keep up with the latest trends in software engineering. And you can, of course, always try to look for specific patterns in bug reports and report vulnerabilities on your own.
3107 Views













