The World of Social Engineering When Vishing and Smishing Attack
By: SmallBizClub

Have you ever received a phone call from someone pretending to be your banker or phone company only to discover it was a scam? Hackers are pretty bold and they are definitely okay with lying to you to gain your trust. They know if they build a relationship especially that you will probably hand your personal information right over to them. That’s why there’s a new category of phishing called “spear phishing” in which high-value employees of a target company become targets of phishing attacks in order to gain access.
Unlike what you see in the movies, hacking is often low-tech. If hackers want to infiltrate a company they just need to look for the weakest point. That’s why the Target hack last year came from printer drivers- who would be on the lookout for malware in printer drivers? But that’s all they needed to gain access to millions of customer credit card numbers. There are any number of ways hackers can gain access to your company by targeting your employees—humans are, after all, the weakest link in security. A hacker could pose as an old high school friend of an employee online—that’s typically what’s going on when you get multiple friend requests from the same person—and strike up a conversation. Remember senior prom? That was a great party. Who do you work for again? What’s your work email, I’ll send you our class reunion info. From there it’s just a few more steps right into your company’s back door. Five out of 6 large companies have been the target of spear phishing, and that number keeps growing every day. It’s even becoming a problem for smaller companies as hackers refine their techniques!
Other common tactics involve posing as someone from your bank or utility company. Sometimes hackers will start by calling your utility company and posing as you or your spouse to get more information about you. Even if they can’t gain access with this technique they can get enough information to successfully fool you into thinking they are legitimate when they do call you. If someone already has your email address and account number, would you really even question it? Hackers are counting on having just enough information on you to get you to give up the information they want, because they know you will do it.
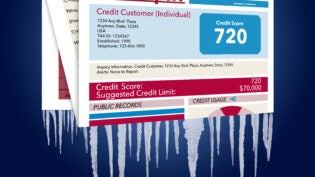
Learn more about phishing, vishing, and smishing from this infographic. You might be surprised just how easy it really is!

Source: ConsumerProtect.com
 Author: NowSourcing is an award-winning nationally recognized infographic design agency. Founded in 2005, NowSourcing has strong roots in the human and technical nuances of the web.
Author: NowSourcing is an award-winning nationally recognized infographic design agency. Founded in 2005, NowSourcing has strong roots in the human and technical nuances of the web.